Top 10 Tips on How to Identify Phishing Emails and Links
Phishing Links, Phishing Emails
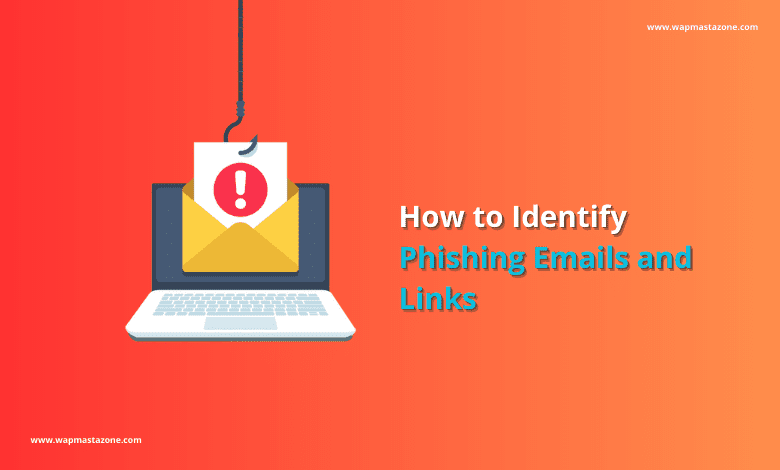
According to Splunk, Around 3.4 billion phishing emails are sent every day, while most of them are automated and targeted at a large audience with weak security or less awareness about internet security.
It is also estimated that 33 million data records are expected to be compromised due to phishing attacks by the end of 2023. Phishing attacks have become increasingly common in recent years, and they pose a significant threat to individuals and organizations alike. These attacks are designed to trick victims into revealing sensitive information, such as usernames, passwords, and credit card details, by masquerading as a trustworthy entity.
Also read: 6 Ultimate Dangers of Using Free Public WiFi
What is Phishing?
Phishing is a social engineering technique that involves the use of fraudulent communication, typically an email or a text message, to trick individuals into disclosing sensitive information such as passwords, credit card numbers, or bank account details. Phishing attacks are usually carried out by cyber criminals who create a fake website or a fake login page that looks like a legitimate website, in order to trick their victims into giving away their confidential information.
If you are someone that pays attention and is very careful, it will be easy for you to identify Phishing emails. It often contains a sense of urgency, a request for personal information, or a fake link that redirects the victim to a fake website. The goal of the attacker is to obtain sensitive information that can be used for identity theft or financial gain. Once the attacker has obtained the information, they can use it to steal money, access confidential information, or confiscate your computer or smartphone.
Also Read: 10 Signs of a Malware Infection on your Computer
10 Tips on How to Identify Phishing Links
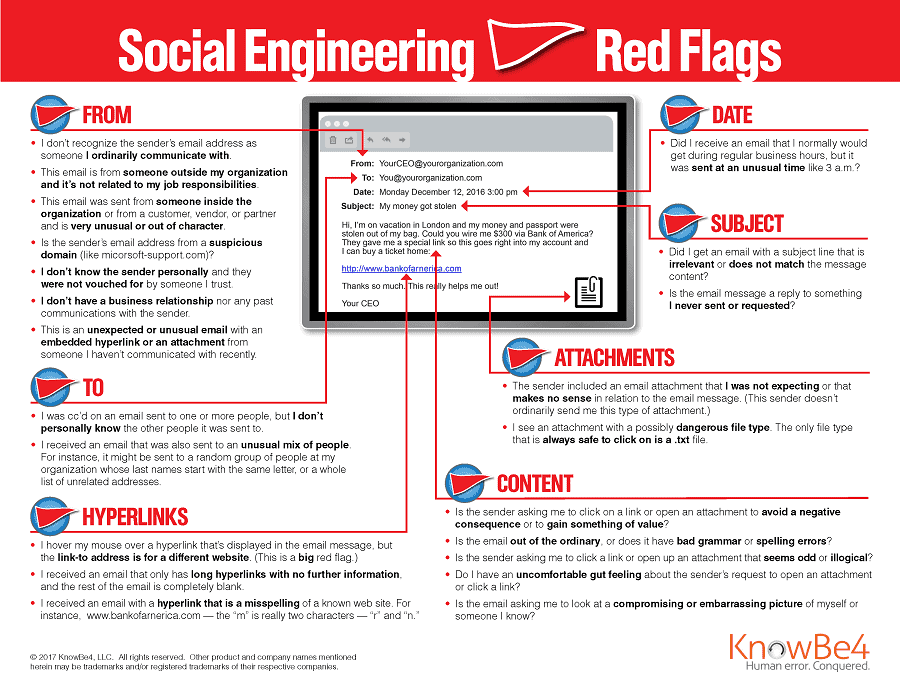
1. Scrutinize the Sender’s Email Address:
Phishing emails are very tricky and can be difficult to identify if you are not very careful. One of the most common tactics used in phishing attacks is to use a fake email address that closely resembles a legitimate one. Therefore, always check the sender’s email address carefully. If it looks suspicious, do not click on any links or download any of the attachments sent to you from the attacker.
2. Be Wary of Urgent Requests:
Phishing emails often create a sense of urgency to encourage the victim to act quickly without thinking. If you receive an email that requires immediate action, pause and assess the situation before taking any action. In every situation, be calm.
Suggested read: Pegasus Spyware – The Most Intelligent Spyware Ever Built
3. Check for Spelling and Grammar Mistakes:
Phishing emails often contain spelling and grammar mistakes, which can be a red flag. The attackers tend to make grammatical mistakes in their messages because they are always in a hurry. Legitimate organizations will usually have a proofreader to ensure that their emails are grammatically correct and free of errors before sending them out.
4. Hover Over Links to Reveal the Destination:
Hovering over a link in an email can reveal its destination. Check the destination URL carefully to ensure that it matches the address of the legitimate website. If the link does not match or contains a suspicious domain name, do not click on it. Sometimes, the link may look legitimate but deadly.
Also read: Internet Security Threats to Watch for
Also read: How to Stay Safe On The Internet
5. Don’t be Quick to Open Attachments:

Attachments can contain malware, so do not open any attachments from unknown sources or those that seem suspicious. If you were not expecting an attachment, it is best to delete the mail/message without opening it.
6. Verify the Request:
If an email requests personal information, be sure to verify the request by contacting the organization directly. Do not respond to the email, use the phone number or website that you know to be legitimate.
7. Watch Out for Threats :
Phishing emails may contain threats or scare tactics to intimidate the recipient into taking action. These threats can include legal action or account suspension. If you receive an email that threatens any action, check the legitimacy of the claim before taking any action.
Also read: 6 Password Safety Tips you Should Never Ignore
8. Beware of Suspicious Links:
Phishing emails may contain links that seem legitimate but lead to fake login pages designed to steal login credentials. Verify the authenticity of any links by typing the address directly into your browser or by contacting the organization directly. One way to do this, which is not the best option is to;
- right click on the link and copy the link,
- then open a different browser that you do not use often, then open the browser in an “incognito mode“
- you can then try to access the link from an incognito mode
- whichever way the link behaves should let you know if it’s a phishing link
- however, you should not use this message if you are not very tech-savvy as you can mistakenly click on the link while following the process.
9. Keep Your Software Up to Date:
keeping your software and applications up to date can prevent attackers from exploiting known vulnerabilities. Regularly update your operating system, web browser, and other software to ensure that you are running the latest security patches.
10. Use Two-Factor Authentication:
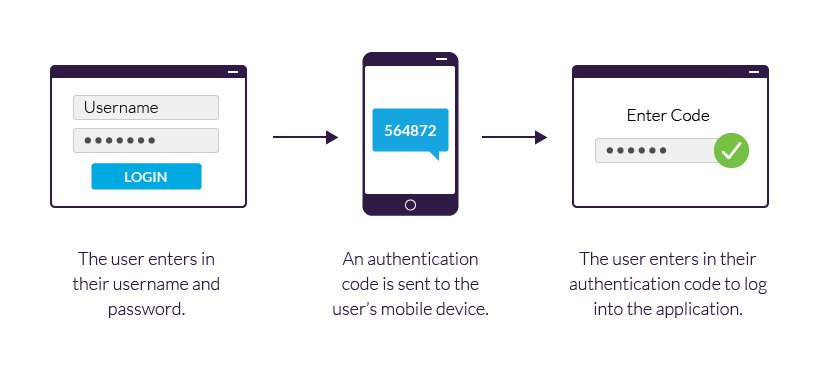
Two-factor authentication adds an extra layer of security to your accounts. This feature requires a second form of authentication, such as a text message or fingerprint scan, in addition to your password. This makes it much more difficult for attackers to gain access to your accounts, even if they have already hijacked your password.
Recommended: 15 Best Free VPN for Android, iPhone and Computer Users
What You Should do if you Have Already Clicked on a Phishing Email or Link
It is very difficult to establish if your computer or smartphone has been compromised immediately after clicking on a phishing email or link because the attacks take different forms.
However, below are some immediate steps you should take after mistakenly clicking on a phishing link or email.
- Disconnect from the internet as this will immediately disallow the attacker from remote access.
- While offline, Run a deep/full scan through your computer antivirus
- Go to installed applications and filter my recently installed ones. Delete/uninstall any recently installed applications that you are not familiar with.
- Restart your device after a deep scan
- If possible, access your email from another secured device and change your email password and any other password that you think could have been compromised
- Also deleted any suspicious emails from your inbox
- If this happened at your workplace, inform the IT department immediately so they can take swift action
Suggested read: How to Prevent Facebook Hack – Complete Guide
Suggestions to Prevent Getting Hacked
Ensure your antivirus is always active and running. You can also install an ad blocker that will block automated web links if you mistakenly visit an untrusted website.
How to Prevent Being Monitored by Spywares
- Use strong VPN
- Update your device once new OS updates become stable.
- Do not open untrusted links and do not use unsecured websites “http://” unless you are absolutely sure or know what you are doing.
- Don’t download untrusted applications or software.
- Check your phone usage and applications frequently.
- Avoid using public or free WiFi
- Use a strong password and multi-factor authentication
- Updates your password when necessary.
We Recommend: Best Virtual Private Network Providers (VPN)
Best VPNs Categories Websites ![]() Securi
SecuriVPN/Internet Security https://www.securi.net/ ![]() CyberGhost
CyberGhostVPN/Internet Security https://www.cyberghost.com/ ![]() PrivadoVPN
PrivadoVPNVPN/Internet Security https://privadovpn.com/ ![]() AtlasVPN
AtlasVPNVPN/Internet Security https://atlasvpn.com/ ![]() Avast
AvastVPN/Internet Security https://www.avast.com/ ![]() IPVanish
IPVanishVPN/Internet Security https://www.ipvanish.com/ ![]() AVG
AVGVPN/Internet Security https://www.avg.com/ ![]() Nord VPN
Nord VPNVPN/Internet Security https://nordvpn.com/ ![]() ExpressVPN
ExpressVPNVPN/Internet Security https://www.expressvpn.com/ ![]() Norton
NortonVPN/Internet Security https://www.norton.com/
Suggested read: Google Indexing and How Web Crawler Works